Applications

Forrester Total Economic Impact of Tanium
The Forrester Consulting Total Economic Impact™ (TEI) study commissioned by Tanium helps technology...

Understanding Augmented and Virtual Reality
In the book, A Whole New Mind: Why Right-Brainers Will Rule the Future, author Daniel Pink describes...

The Definitive Guide to Sharepoint Migration Planning
If I've learned anything in more than a decade of working with SharePoint, it's that migration is more...
Multi-Factor Authentication Guide to On-Premise MFA
Despite the advantages of moving to the cloud and in spite of security assurances, there are still organisations...
5 steps to successfully deploying a healthy CMDB
Your path to total service visibility and great service availability. Your CMDB is a critical tool for...

Best Practices for Deploying Huddle Rooms in the Enterprise
The 20th century was the Information Age, in which companies with access to the most relevant and timely...
MIT Executive Guide: The AI and Machine Learning Imperative
Companies across various industries are seeking to integrate AI and machine learning (ML) into workflows...

Guide to Strengthening Mainframe Security
Successful phishing attacks lead to a loss of control over user IDs, passwords and credentials. Bad actors...

Powering your organisation with an agile productivity stack
I wonder where our important files have run off to today.' When you've got one seamless, secure platform...

Q&A: First Steps to a World-class Digital Workspace Experience
Most companies today measure the success of workspace initiatives using tangible cost benefits that are...

The Definitive Guide to Migrating to the Cloud
To lay the foundation for modern application development, increase agility, and reduce cost, IT leaders...
The Inner Circle Guide to Agent Engagement and Empowerment
Your agents aren't going to ask you for more automated tools, empowered and personalized coaching, and...
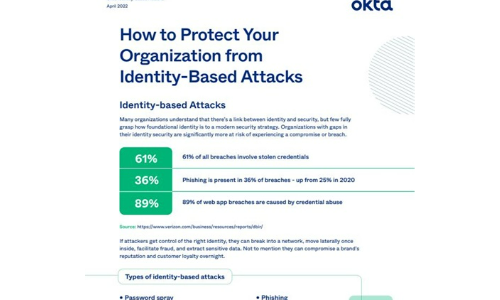
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...

Lacework 2021 Cloud Threat Report, Volume 1
The Lacework Labs team provides quarterly reports focused on risks and threats relevant to cloud services,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.