Backhaul

Getting Started with SASE
Secure Access Service Edge: A guide to secure and streamline your network infrastructure As enterprises...

Definitive Guide to Internet Isolation
The traditional approach to cybersecurity has reached its potential, and attackers have learned how to...

3 Secrets to SD-WAN Success
Organizations are turning to software-defined wide area networks (SD-WAN) to intelligently route traffic...

SASE: Beyond the Hype
Solve network and security management challenges with a Secure Access Service Edge architecture This...
Cloud networks: Shifting into Hyperdrive
Public cloud is driving digital innovation. As IT organizations around the world continue to radically...
DDoS Attack Threat Landscape — Tracking DDoS Attack Trends in Q2'22
DDoS attacks are on the rise. Ransom attacks reached an all-time high in June 2022, the Ukraine-Russia...
What makes a 5G Leader?
With 5G a still nascent technology, opportunity remains for businesses to accelerate adoption of this...
Connected cities and places
Improving digital infrastructure is key to enabling a smarter city or place to develop, thereby creating...

Core connectivity: The key enabler of digital transformation
The phrase 'digital transformation' is a hot topic across industry right now. Based on the consultancy...

EMA Report: Availability and Buying Options in the Emerging SASE Market
Cloudflare One reviewed as a leading provider of Secure Access Service Edge Gartner's Secure Access Service...
Multi-cloud Load Balancing for Dummies
Legacy hardware-based load balancers don't meet modern enterprise application delivery requirements in...
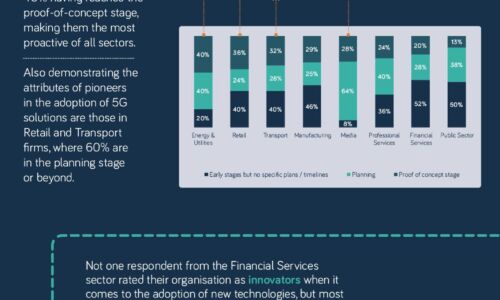
The 5G opportunity within UK industry
Neos Networks research shows that two thirds of organisations expect to have made significant investment...

The challenges and opportunities for smart cities
With urbanisation continuing at breakneck speed around the world, governments need solutions to make...
Implementing the NIST Zero Trust Architecture with Zscaler
The National Institute of Standards and Technology (NIST) has defined the core components of zero trust...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.