Data Center
Inside Complex Ransomware Operations and the Ransomware Economy
Ransomware operators have steadily become more sophisticated and more aligned with nation-state actors,...

Open Channels, Hidden Threats
How Communication and Social Media Tools Are Changing the Insider Risk Equation for Compliance, IT and...
A CIO's Guide to Accelerating Secure Digital Transformation
Cloud transformation is imperative, and it's the CIO who is under pressure to make sure the business...
Avoiding Container Vulnerabilities
Containers offer an unprecedented opportunity to scale cloud-based services, make incremental changes...
APIs For Dummies
APIs are a hot topic, energetically debated by businesspeople, IT managers, and developers alike. Most...
CIO Priorities: Forcing Business to Evolve
It's apparent now that the forces pushing for businesses to embrace technology to modernization are unstoppable....

Cybersecurity strategies need to evolve.
Over the past 20 years, cybersecurity strategies have primarily focused on protecting the network perimeter...
The Virtual Floorplan: New Rules for a New Era of Work
The Virtual Floorplan: New Rules for a New Era of Work is a global report analyzing hybrid work, and...
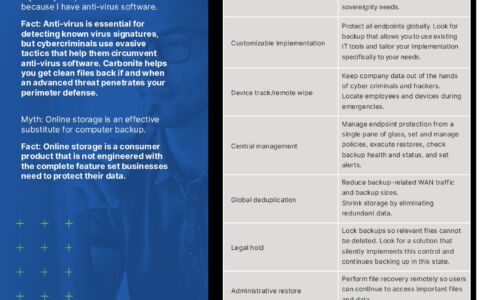
Carbonite Endpoint Protection Myths
Myth: My endpoint data is secure because I have anti-virus software. Myth: Online storage is an effective...

Zero Trust Access for Dummies
As businesses continue to embrace digital innovation, cloud applications, and the new work-from-anywhere...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.