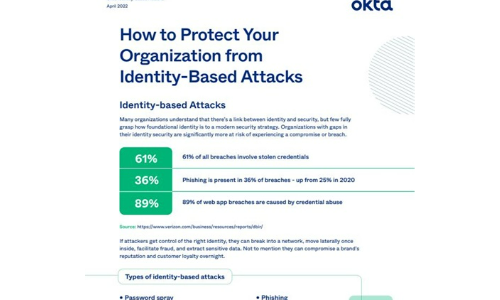
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...

Change management blueprint for contact centre digital transformation
The COVID-19 pandemic put organisational change into hyperdrive. Businesses were compelled to move to...

Find and Protect Your Sensitive Data with SQL Server Compliance Tools
This technical brief examines a database compliance and security scenario in the enterprise. It describes...

Three key strategies for customer experience success
Get customers banking on you with seamless collaboration. The importance of working seamlessly with people...

Drive business growth with personalization
Personalizing content for a customer online is key to breaking through the noise. Yet brands face challenges...

Brilliant Experiences, Channel by Channel
Communicating in ways that speak to each individual customer, is what allows brands to build strong relationships....

Why you need an adaptive security segmentation solution
The threat landscape is more dynamic than ever before, and as business-critical applications traverse...
Finding a platform worthy of your data
Attacks on your data are getting trickier, and insider threats are on the rise. More than half of IT...

CISSP For Dummies
Secure your CISSP certification! If you're a security professional seeking your CISSP certification,...

Two-Factor Authentication Evaluation Guide
In this guide, you will learn how to evaluate a solution based on: ...

Six Steps to Intelligent Data Privacy
Explosive data growth is a double-edged sword. On one hand, it's enabling the most disruptive and exciting...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


