ERP
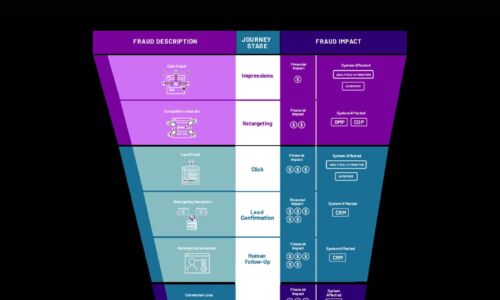
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....

CIO Roadmap to Hybrid and Multi-Cloud
While cloud has become a key driver of business expansion and operational efficiency, business and IT...

SASE-Ready WAN Edge for the Work from Anywhere Era
Enterprise networks are on the verge of a major tipping point, driven by the shift from employees working...

The Data Governance Program Workbook
If you're reading this, then you've already made some important decisions. You've decided to invest in...

6 Lessons for Cybersecurity Leaders
The state of security is highly adrenalized these days — more so than usual. Years into the deadly...

Dell Technologies Data Protection Portfolio
In the past few years, the IT landscape has seen many profound changes and evolutions fueled by a combination...
The Role of Machine Learning and Automation in Storage
There has been lots of hype around the increasing role that machine learning, and artificial intelligence...
2020 Cost of Insider Threats: Global Report
The average global cost of insider threats rose by 31% in two years to $11.45 million. And the frequency...
The Difference Between API Gateways and Service Mesh
In this eBook, Kong Inc Co-Founder and CTO Marco Palladino illustrates the differences between API gateways...

Extracting the Full Value of the Cloud
As more enterprises move their IT infrastructures to the cloud and get their software via cloud subscriptions,...
Four Reasons to Rethink Your ERP Vendor
Read this guide for everything you need to know about enterprise cloud applications, the questions you...

IT's 5 Toughest Work from Home Challenges
All of a sudden, you (and everyone else) found yourself working from home (WFH). The one advantage was...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

