Firewall
Beyond on-demand for DDoS defense
The global pandemic changed the way we work, travel, play, and stay connected — increasing our reliance...
Making the Grade: End-to-End Security in Education
While students are preoccupied with completing online school assignments and streaming educational videos,...

DynamoDB Users-Why Switching to Couchbase Will Save You Time and Money
Businesses using the Amazon Web Services (AWS) cloud often store their data in Amazon's DynamoDB database...

KuppingerCole Leadership Compass
Leaders in innovation, product features, and market reach for access governance and intelligence. Delivering...
Enhanced Privilege Access Management Solutions
Privileged Access Management (PAM) is one of the most important areas of risk management and security...

We've saved time, money and resource
Come and see how we upgraded our ServiceNow production instance to Paris in 28 hours and learn how Motorola...

Getting started with SASE:
Secure Access Service Edge: A guide to secure and streamline your network infrastructure As enterprises...

The Beginner's Guide to Dynamic Case Management
What is dynamic case management? Who is using it and how can it help you prepare for the future of work? The...

Data to Decisions
If any company still questioned the central importance of data to its future prospects, the last month...
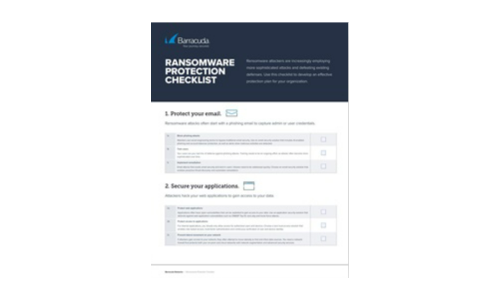
Ransomware Protection Checklist
Ransomware attackers are increasingly employing more sophisticated attacks and defeating existing defenses....
The Three Keys to Secure and Successful Cloud Migrations
To make cloud transformations as efficient and successful as possible, companies must remain secure and...
Application security, fallacies + realities
The news headlines have been filled with stories about security breaches in recent months. And most of...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

