IT Management

Ransomware Protection with Veritas NetBackup Appliances
Download this whitepaper to discover how to protect your backup and recovery infrastructure from attacks....

Forrester Wave Report
In our 33-criteria evaluation of web application firewall (WAF) vendors, we identified the 10 most significant...

When Networks Meet The New Tomorrow
This paper looks at IT priorities that organizations will need to address now and in the new tomorrow: +...
How 5 Enterprises Consolidated ITSM to Reduce Costs
See how five leading brands modernized ITSM with ServiceNow. For businesses that want to transform, modernizing...
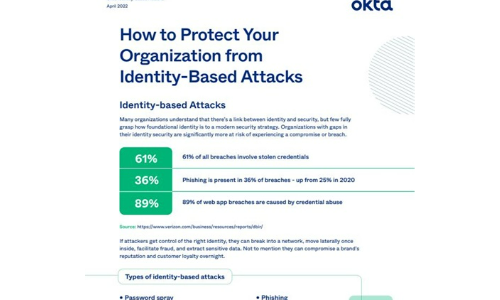
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...

Security Control Guide: Hardened Services Guide
System Hardening is the process of securing a system's configuration and settings to reduce IT vulnerability...
Break down data silos
Make data available to anyone at any time. To make decisions quickly, organizations will want to store...
The Three Keys to Secure and Successful Cloud Migrations
To make cloud transformations as efficient and successful as possible, companies must remain secure and...

Zero Trust: The perfect solution for the perfect security storm
We're experiencing a classic example of the perfect storm. Never have organizations faced so many challenges...

Securing Microsoft 365
Few tools are as critical to modern business as Microsoft 365. Unfortunately, the platform's ubiquity...

5G for Dummies
5G, the next iteration of wireless networks, is not merely an incremental increase in network speed and...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


