Mobile Computing
Risk-Adaptive Data Security: The Behavior-Based Approach
This eBook addresses the challenge with DLP of either applying restrictive policies which slow down the...

2021 State of the Threat in review
The State of the Threat report is compiled by the world-renowned Secureworks® Counter Threat Unit™...
DEIB Analytics: A Guide to Why and How to Get Started
Gain insights from RedThread Research on why businesses are focused on diversity, equity, inclusion and...

How to Get Real Value from AI in Data Analytics
Increasingly, Artificial Intelligence is showing up in the products we use and the activities we engage...

IT’s 5 Toughest Work from Home Challenges and How to Solve Them
2020 forced the shift to a hybrid work model Unexpectedly, you found yourself working from home. The...

The PC Lifecycle Continuum: From Control to Transformation
As diverse organizations seek to implement data-driven strategies, the personal computer in all its varieties...
Penetration Testing For Dummies
Target, test, analyze, and report on security vulnerabilities with pen-testing Pen-Testing is necessary...

Multicloud and Hybrid Cloud
This pathfinder paper navigates decision-makers through the issues surrounding multicloud and hybrid...

Moor Insights: Cloud is Built on Modern Infrastructure
The modern enterprise lives in a multi-cloud world, where delivery of infrastructure resources and IT...
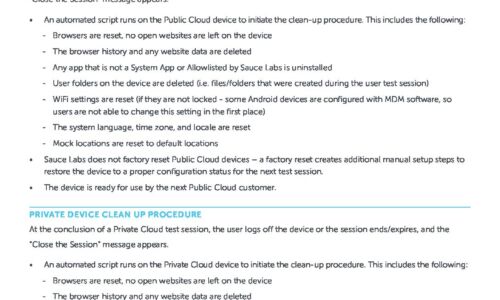
Public & Private Device Clean Up Procedure
This data sheet explains the options available when you want to make sure that your content, or some...
An Overview of Insider Threat Management
As organistions move towards a more distributed workforce, the traditional perimeter of the office network...

Empowering Medical Manufacturers to Become Leaders
Due to increasing technology and product complexity, regulatory requirements and supply chain issues,...

IT's 5 Toughest Work from Home Challenges and How to Solve Them
2020 forced the shift to a hybrid work model Unexpectedly, you found yourself working from home. The...

Common Browser Isolation Challenges and How to Overcome Them
Every security team wants to keep their employees and data safe from the latest threats. To accomplish...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.