Software
The Mimecast-Netskope-CrowdStrike Triple Play
Security and IT organizations must protect against new attacks at scale — and safeguard data in use,...

Secure Beyond Breach
Securing the perimeter is no longer enough. The focus has shifted to ensuring your organization continues...

Valoir Report: Third-Party Support Goes Mainstream
Adoption of third-party support for enterprise software is now mainstream. In a report sponsored by Rimini...

A More Effective CIO-CFO Partnership
How are IT leaders achieving success in a changing world? To find out, Deloitte and Workday surveyed...

The Forrester Wave™: DDoS Mitigation Solutions, Q1 2021
Cloudflare Named A 'Leader' in The Forrester Wave™: DDoS Mitigation Solutions, Q1 2021 Forrester Research,...

The PMO that delivers
A modern PMO is no longer project focused, it is business focused. Instead of trying to ensure projects...
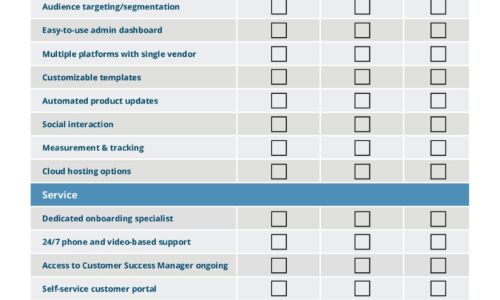
IT Comms Plan Bundle
IT teams need to communicate important messages across their organization – from scheduled maintenance...
Take control of diverse and rapidly evolving enterprise risks
Today's enterprises face diverse and rapidly evolving risks, including expanding regulatory requirements,...

3 steps to reducing software, hardware and cloud costs
Your technology teams are under more pressure than ever to rapidly transform the business. But how do...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.




