Windows Server

Top 10 Reasons to Partner with Dell EMC for Windows Server 2016
The release of any Microsoft operating system is always an important crossroads for IT decision-makers,...

Run your Windows workloads on AWS
The best platform for Windows Server and Microsoft SQL Server Customers have been running Windows workloads...

VMware Multi-Cloud Architecture: Enabling Choice and Flexibility
In today's world, application growth is unprecedented and enterprise applications on a wide range of...

Using MITRE ATTandCK™ in Threat Hunting and Detection
MITRE ATTandCK ™ is an open framework and knowledge base of adversary tactics and techniques based...
Upgrade to State-of-the-Art Log Management
Most log messages traditionally come from three types: system logs of servers, network devices, and applications....

High-performance persistent storage for virtualized workloads
Supporting virtualized workloads in Red Hat® OpenShift® requires reliable persistent storage that offers...

Using MITRE ATT&CK™ in Threat Hunting and Detection
MITRE ATT&CK ™ is an open framework and knowledge base of adversary tactics and techniques based on...

Ransomware Prevention Is Possible
Ransomware is a form of malware that encrypts files to prevent victims from accessing their systems and...
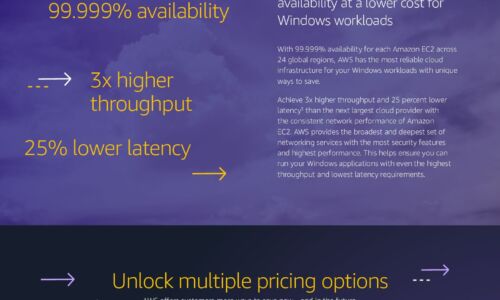
Windows Cost Savings Infographic
Save by moving Windows workloads to AWS Companies can lower infrastructure costs while improving performance,...

2019 IT Skills and Salary Report
The 2019 IT Skills and Salary Report provides the most informative and revealing insights into the inner...

The IT Salary and Skills Report 2017 (100 Page Full eBook)
What does your industry look like? Download this comprehensive IT industry salary report, with data from...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


