Latest Whitepapers
Eight Critical Practice Areas That Drive Multi-Cloud Use Maturity
While most organizations are already using two or more clouds, most teams within the larger organization...

Building the Business Case for Improving Endpoint Security
As a security provider, we understand that convincing executives to make changes to their stack can be...
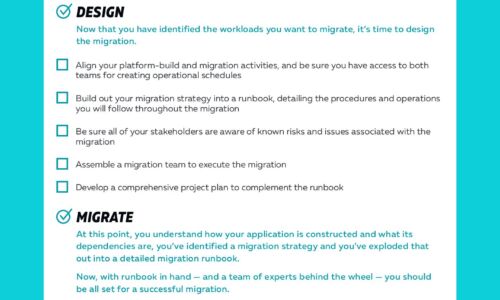
Cloud Migrations Checklist
Cloud migrations can be complex. The key to a successful migration lies in the planning. To help, we've...

6 Trends ITSMs Must Address
Businesses in the IT Service Management (ITSM) sector are undergoing significant change. VARs, MSPs and...

The Fastest Way to Modernize Apps Isn’t What You Think
When it comes to digital transformation, we hold these truths to be really, really evident: • Organizations...

TLS Best Practices
The truth is, a simple lapsed certificate can become a time-consuming headache. Unfortunately, 60% of...

Maintaining ‘Business As Usual' In Unusual Circumstances
The phrase 'business as usual' has a reassuring quality. It represents an ideal state in which the company...

PHP, MySQL, & JavaScript All-in-One For Dummies
Get the basics on four key web programming tools in one great book! PHP, JavaScript, and HTML5 are essential...

Elastic Cloud Gateways: The Evolution of Secure Cloud Access
Enterprise security groups today face a daunting task. While their core responsibility of protecting...

Public and Private Device Clean Up Procedure
This data sheet explains the options available when you want to make sure that your content, or some...

Cloud Security Report 2022
Cloud adoption continues to permeate throughout organizations as they embrace agile software development....
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.








