Latest Whitepapers
The role of CIO in a world where experience rules
In recent years, the role of CIO has evolved to meet a wider set of responsibilities and aspirations....

10 Security Tips for Businesses
SECURITY THAT PROTECTS YOUR BUDGET Vanishing budgets, reckless users, infected machines, unpatched software...

Interpublic Group Adds Business Value to its Companies Through Security
Interpublic Group (IPG) is a premier global advertising and marketing services enterprise. Its companies...

Improve Productivity with Box and Office 365
In this guide, discover why Box is the perfect complement to Office 365 — and all the other apps you...

The New Future of Work
To address the challenges of 2020 and emerge stronger in this New Future of Work organisations need to...

The Modern Mailer
The world of print and postal communications is changing. With reducing average run lengths and the ongoing...

Lessons from past vulnerability exploits and how WAF can help
Fight web attacks in seconds without slowing down your website. The onset of 2020 was marked by the disclosure...
Understanding Secure Access Service Edge (SASE) Architectures
Secure Access Services Edge (SASE) aims to replace traditional, hub-and-spoke architectures with secure...

Innovating in the Exponential Economy: Chapter 2
For all businesses, innovation is crucial for competitiveness and survival but it is notoriously hard...
Securely Enabling a Hybrid Cloud in Microsoft Azure
The public cloud has rapidly moved past the novelty, curiosity stage to the business critical initiative...
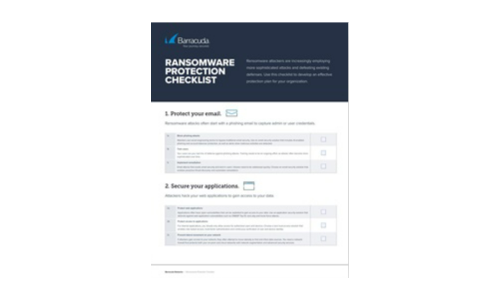
Ransomware Protection Checklist
Ransomware attackers are increasingly employing more sophisticated attacks and defeating existing defenses....
Making the Grade: End-to-End Security in Education
While students are preoccupied with completing online school assignments and streaming educational videos,...
The Total Economic Impact™ Of ServiceNow Field Service Management
ServiceNow® Field Service Management is a cloud-based solution that connects field service to other...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.






