Cloud Computing
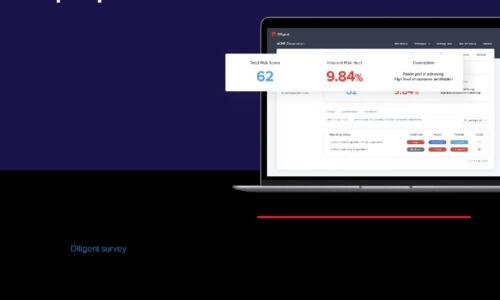
Effective CISO Presentations to the Board: Top Tips & Checklist
As a CISO, you have crucial info to convey about cyber risk, and your board wants to hear it. In a recent...
Refine your data strategy
Get more out of data and machine learning. Data, analytics, and machine learning have the potential to...
Can ZTNA replace your VPN?
Compare 3 remote access approaches Seamless remote access enables companies to boost employee productivity...

Project Portfolio Management 101
Is your organization adopting new technologies, processes, or services to better compete in the marketplace...

Four Tenets to Guide Your Enterprise's Cloud Transformation
Company leaders are increasingly turning to multi-cloud to deliver applications and other infrastructure...
Cyber Risk Commands C-suite's Focus: The State of Email Security 2023
As companies grow more skittish over rising economic volatility and intensifying geopolitical tensions,...

Managing Mainframe Phishing Vulnerabilities
Mainframes are undisputedly the most mature, secure and best defended computing platform. Yet even mainframes...
Efficacy of Micro-Segmentation: Assessment Report
Micro-segmentation is an essential security control that prevents the lateral movement of attackers....

The Role of Immutable Storage in Ransomware Protection and Recovery
All organizations need to face an unpleasant truth: It is not a question of 'If' they will experience...

Empower End-Users With Better Experiences
Why is end-user computing innovation important? You have a lot of market forces driving your organization,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.