Cloud Computing
Multi-Factor Authentication Guide to On-Premise MFA
Despite the advantages of moving to the cloud and in spite of security assurances, there are still organisations...
Cyber Risk Commands C-suite's Focus: The State of Email Security 2023
As companies grow more skittish over rising economic volatility and intensifying geopolitical tensions,...

Analysing the Economic Benefits of Proofpoint Insider Threat Management
Did you know the average annual cost for insider threats is now $11.45M, according to Ponemon Institute?...

Moor Insights: Cloud is Built on Modern Infrastructure
The modern enterprise lives in a multi-cloud world, where delivery of infrastructure resources and IT...

Seven Strategies to Securely Enable Remote Workers
Is your organisation ready to securely support a wide range of remote workers in the wake of a global...
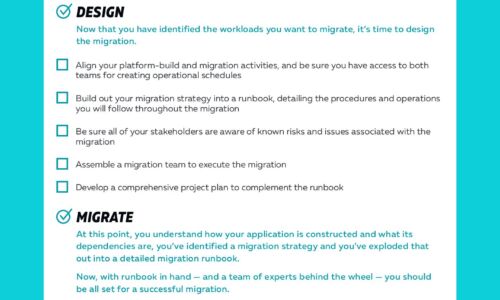
Cloud Migrations Checklist
Cloud migrations can be complex. The key to a successful migration lies in the planning. To help, we've...

The Ultimate Guide to Cyber Hygiene
It's critical for organizations to deeply understand their risk posture and have tools in place that...

Cybersecurity for retail: Prevention is better than the cure
Prevention is almost always better than the cure. But how many organisations are living up to the promise...
Ransomware Protection Checklist
Ransomware attackers are increasingly employing more sophisticated attacks and defeating existing defenses....

Zero Trust Access for Dummies
As businesses continue to embrace digital innovation, cloud applications, and the new work-from-anywhere...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.