Cloud Security
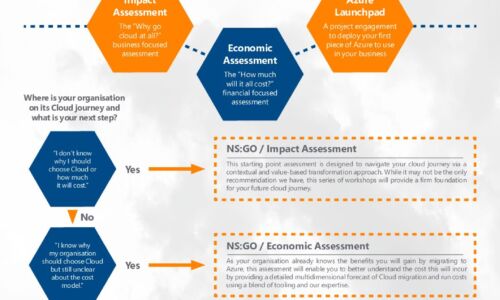
Azure Accelerator kit: Travel in the fast lane with New Signature
At New Signature, we understand that organisations are finding it difficult to start their Public Cloud...

Cloud Cheat Sheet (Amazon vs. Microsoft vs. Google)
Web applications have always been deployed on servers connected to what is now deemed the 'cloud'. But...
Stopping BEC and EAC
Business email compromise (BEC) and email account compromise (EAC) are complex problems that require...

Elastic Cloud Gateways: The Evolution of Secure Cloud Access
Enterprise security groups today face a daunting task. While their core responsibility of protecting...

Cyber Attack Trends: Check Point’s 2022 Mid-Year Report
The war in Ukraine has dominated the headlines in the first half of 2022 and we can only hope that it...
Making the Case for A Workstation-Centered Workflow
A hybrid computing approach with the workstation at its center is the most efficient workflow for professional...

Migrating Apps to the Cloud in 5 Steps
Cloud applications, platforms and services are changing the way enterprises compete for customers. The...

Build Your Cloud Security Skills to Innovate with Confidence
How security training from AWS can help you boldly pursue your biggest cloud goals Today, security is...

7 Steps to Developing a Cloud Security Plan
Security concerns are top-of-mind for IT executives in light of highly publicized data breaches at a...

Top 3 challenges your team faces when building in the cloud
Learn the root causes of the challenges your cloud and security teams are facing and see how these challenges...
Cloud Report: Cloud Services
In this Netskope Cloud Report™, we've compiled the most interesting trends on cloud service and web...

Reduce Alert Fatigue in Your IT Environment
Security teams are tasked with managing a huge volume of alert logs, and this noise can overwhelm any...
Cloud Workload Protection
The hybrid cloud is at the centerpiece of digital transformation. Today, more than 90 percent of enterprises...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
