Cloud Security

EMA Report: Availability and Buying Options in the Emerging SASE Market
Cloudflare One reviewed as a leading provider of Secure Access Service Edge Gartner's Secure Access Service...
How to Build Your Microsegmentation Strategy in 5 Steps
A breach to your organization's network is not a question of if, but when. Are you prepared with a micro-segmentation...

Addressing Multiple Concerns with a Single Solution
Organizations have been steadily implementing digital innovations for years, but recently the pace of...

AWS Cloud Operations
Built for operating at cloud scale, AWS Cloud Operations offer a clear and easy path to the business...
Making the Case for A Workstation-Centered Workflow
A hybrid computing approach with the workstation at its center is the most efficient workflow for professional...
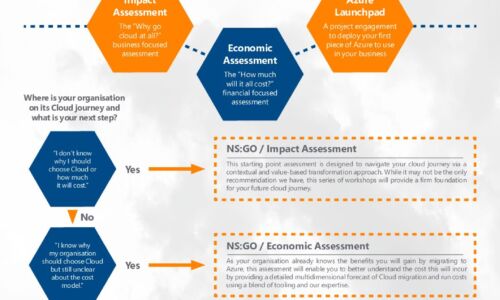
Azure Accelerator kit: Travel in the fast lane with New Signature
At New Signature, we understand that organisations are finding it difficult to start their Public Cloud...

Speed Up Your Digital Transformation With The Cloud
In this Content Services in the Cloud Guide by AIIM, we explore how companies are tackling critical document...

Go Mainstream with SD-WAN: Migration Best Practices
Over the last couple of years, SD-WAN technology has matured into a mainstream solution. Yet, the most...

Python for Data Science For Dummies, 2nd Edition
The fast and easy way to learn Python programming and statistics Python For Data Science For Dummies...
Powering Digital Transformation With A Hybrid Cloud Strategy
Today's organizations are looking closely at how to optimize their existing application portfolios, and...

Reinvention Starts with Cloud Migration of Data Infrastructure
Take the complexity out of your data infrastructure For organizations running legacy data infrastructure...

Top 3 Security Considerations for the Cloud
Data centers are evolving to include a mix of static hardware and cloud computing technologies. However,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

