Data Center
Technical buyer's guide to site search
Consumer-grade search is one of the hardest feature to get right as it includes multiple disciplines...

Low-Code and No-Code: Automation for the Modern Organization
As the adoption of no-code and low-code development solutions grows, many users have questions around...

Your guide to small office IT success
Providing a great IT experience for your office doesn't have to be a challenge. Illustrating different...

Mitigating Information Security Risks in Microsoft 365
Microsoft 365 offers multiple tiers of capabilities that all leverage the cloud to enable professionals...

The Perimeter's Gone. Can Your Security Handle It?
Organizations need to shift their security strategy to secure the new ways work gets done. That takes...
Internal Firewalls for Dummies Guide
Organizations can no longer rely on edge firewalls alone to provide network security. Once attackers...

A Buyer’s Guide to Optimizing Remote Employees’ Extended Network
The shelter-in-place mandates put in place earlier in 2020 sent most employees home, and for the next...

MSP Security Best Practices: Ransomware Attack Prevention
In Datto's Global State of the Channel Ransomware Report, 4 in 5 managed service providers (MSPs) agreed...

2020 CIO Cloud Data Management Initiatives
According to the results of Frost and Sullivan's Digital Transformation survey, 99% of businesses are...
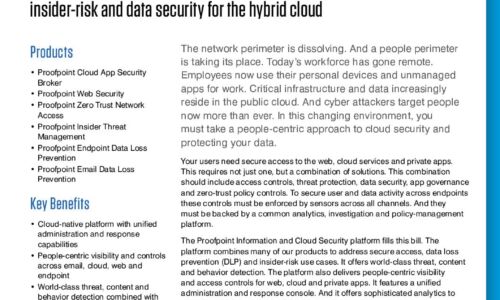
Proofpoint Information and Cloud Security Platform
The Proofpoint Information and Cloud Security platform combines many of our products to address secure...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.