Network

The Essential Guide To Machine Data
Machine data is one of the most underused and undervalued assets of any organization, yet it contains...
Understanding Secure Access Service Edge (SASE) Architectures
Secure Access Services Edge (SASE) aims to replace traditional, hub-and-spoke architectures with secure...

Pure Storage FlashRecover, Powered by Cohesity
Data continues to grow at an unprecedented rate, and the rise in the value and volume of data has coincided...

Enhancing Microsoft Security with HelpSystems Email Security
Learn how HelpSystems Email Security can enhance Microsoft 365. Microsoft 365 offers tiers of security...

State of Digital Transformation EMEA 2020
Prior to the pandemic, enterprises were actively migrating private applications to public clouds as well...

How to Ensure Flexibility in a Hybrid Multicloud Strategy
Enterprises are moving rapidly to diverse cloud models, including hybrid cloud, multicloud and connected...

Ponemon Cost of Insider Threats Global Report
Independently conducted by Ponemon Institute External attackers aren't the only threats modern organisations...
CISO's Playbook to Cloud Security
To secure enterprise assets in the cloud, CISO's must address several new challenges unseen in traditional...

IT's 5 Toughest Work from Home Challenges and How to Solve Them
2020 forced the shift to a hybrid work model Unexpectedly, you found yourself working from home. The...
Zero-Trust is the Outcome of Identity-Based Access Control
As the IT landscape evolves, new and more sophisticated cybersecurity threats continue to appear. These...
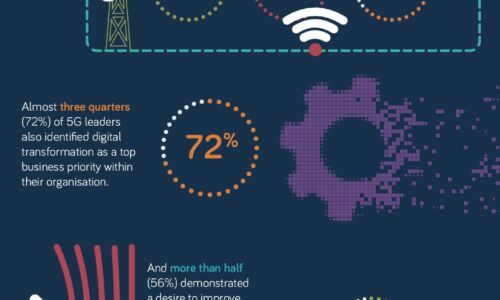
What makes a 5G Leader?
With 5G a still nascent technology, opportunity remains for businesses to accelerate adoption of this...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.