Network

Maintaining ‘Business As Usual’ In Unusual Circumstances
The phrase 'business as usual' has a reassuring quality. It represents an ideal state in which the company...
Red Hat for cloud-native development
Application development is a complicated undertaking that requires a complex environment and tools. With...
Ransomware Survival Guide
Be Ready for Ransomware Ransomware is an old threat that just won't go away. While overall volumes have...

The Cybersecurity fail-safe: Converged Endpoint Management (XEM)
Organisations are experiencing more attacks than ever before. Cybersecurity Ventures expects a ransomware...

Managing Mainframe Phishing Vulnerabilities
Mainframes are undisputedly the most mature, secure and best defended computing platform. Yet even mainframes...
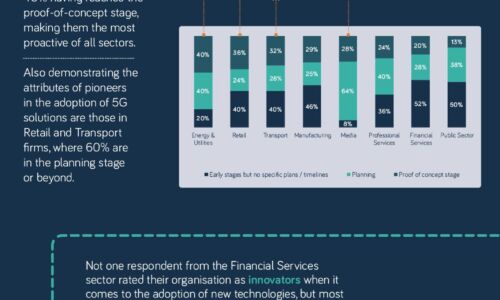
The 5G opportunity within UK industry
Neos Networks research shows that two thirds of organisations expect to have made significant investment...
The Five Nastiest Security Mistakes Exposing Public Cloud Infrastructure
Public cloud infrastructure has become a critical asset to enterprises that compete on innovation. Protecting...

2022 Threat Report
The BlackBerry 2022 Threat Report is not a simple retrospective of the cyberattacks of 2021. It is a...

2022 State of the Threat: A Year in Review
In 2022, ransomware remained the most prevalent form of attack. In investigations by Secureworks® incident...

2022 MSP Threat Report
This report was created by the ConnectWise Cyber Research Unit (CRU)—a dedicated team of ConnectWise...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.