SAN
Eight Critical Practice Areas That Drive Multi-Cloud Use Maturity
While most organizations are already using two or more clouds, most teams within the larger organization...

How to Integrate DocuSign
A smooth integration is key to the success of any digital transformation project. Many organisations...

Valoir Report: Third-Party Support Goes Mainstream
Adoption of third-party support for enterprise software is now mainstream. In a report sponsored by Rimini...
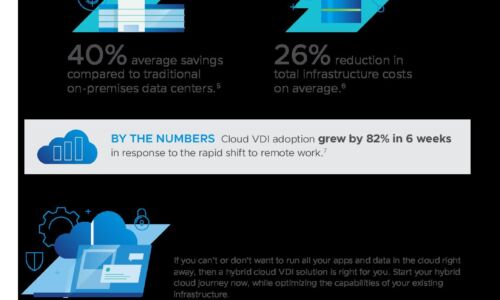
How Virtual Desktop Infrastructure Enables Digital Transformation
Virtual desktop infrastructure (VDI) is a foundational technology that many organizations leverage as...

Protecting Every Edge To Make Hackers' Jobs Harder, Not Yours
Today's users need a network that allows them to connect to any resource from any location using any...

SME Lending: The Road to Real- Time Approvals
How to Build World-Class SME Lending Experiences Thirty-two percent of SMEs now work with online lenders...

The CIO's Guide to Identity Driven Innovation
Today's CIOs are increasingly accountable for more than just enabling the organisation with tools and...
9 Hedge Fund Scandals That Could Have Been Prevented
More often than not, non-compliance and financial misconduct can be caught before it results in substantial...
3 Reasons to Choose Managed Detection and Response
Cyber threats affect data security in all organizations, but organizations in highly regulated industries...
Assessing Network Traffic Analysis (NTA) Requirements
Many organizations are struggling to detect, hunt, investigate, and respond to threats in an efficient...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.