Software

Unified Fast File and Object (UFFO) Storage
In this book, you get an idea of the vast potential for unstructured data — and also the infrastructure...

Spear Phishing: Top Threats and Trends
Cybercriminals are constantly refining their tactics and making their attacks more complicated and difficult...
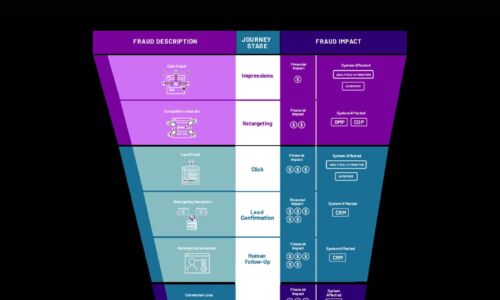
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....

The 7 Hidden Truths of Cloud Security
Based on extensive, up-to-date knowledge and experience from WithSecure consultants, threat hunters and...

2022 agent experience trends report
RingCentral recently teamed up with Benchmark Portal to conduct a survey on contact center agent turnover...

Speed Up Process Change for SAP ERP
The ability to move fast and having a rapid response to change is needed for businesses to innovate faster....

Security and risk management in the wake of the Log4j vulnerability
Security leaders agree: Log4j has irrevocably changed the risk landscape. Get a quick refresher on the...

Definitive Guide to Internet Isolation
The traditional approach to cybersecurity has reached its potential, and attackers have learned how to...
Four Steps to Analytics Governance
Digital Transformation has accelerated through the roof since the beginning of 2020. According to recent...

The PMO that delivers
A modern PMO is no longer project focused, it is business focused. Instead of trying to ensure projects...

Powering Data-Driven Innovation in Fintech
SingleStore is powering some of the most innovative Fintech companies around the world and across multiple...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


