Compliance

Quest® KACE® SMA reduces software license compliance stress
Do you know whether all your software licenses are compliant? Your IT landscape has gotten more and more...
Why It Pays to Use Electronic Signature
In today's intensely competitive marketplace, the business world is moving rapidly to online transactions...

3 Ways to Make Cloud your Business eBook
The role of IT infrastructure and operations leaders has dramatically changed, and cloud evolution continues...

2021 Buyer's Guide to Comprehensive Cloud Security
Cyber resilience comes when you've secured your multi-cloud infrastructure and enabled your DevSecOps...
Charting a Course to SAP Modernization Success
As enterprises plan their SAP modernization efforts, they are looking for solutions that allow them to...
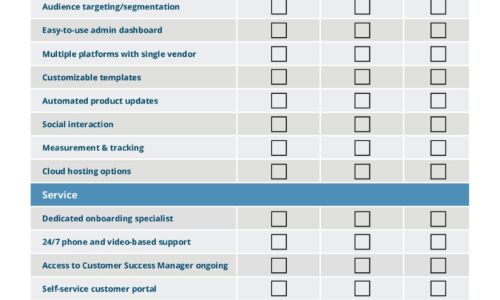
IT Comms Plan Bundle
IT teams need to communicate important messages across their organization – from scheduled maintenance...

2021 Voice Of The CISO Report
There's no question that 2020 was a challenging year. The pandemic placed an enormous strain on the global...

The Total Economic Impact of Adobe Sign
Adobe recently commissioned Forrester Consulting to conduct a Total Economic Impact (TEI) study to help...

GigaOm Radar for Data Storage for Kubernetes
Kubernetes adoption is quickly accelerating, and enterprises are now in a transition phase. In the last...

The Perimeter's Gone. Can Your Security Handle It?
Organizations need to shift their security strategy to secure the new ways work gets done. That takes...

Top 5 Security Concerns in Financial Services
Solving the most critical issues in the most targeted industry. We've created this guide to show you...

How to Ensure Flexibility in a Hybrid Multicloud Strategy
Enterprises are moving rapidly to diverse cloud models, including hybrid cloud, multicloud and connected...

Learning From The Low-code Playbook
Low-code development is proliferating worldwide — but a rift has opened between the early adopters...
Essential Operational Resilience
COVID-19's far-reaching impacts have thrashed many companies' Plan-A strategies, yet the pandemic offers...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.