Data Center

VMware Multi-Cloud Architecture: Enabling Choice and Flexibility
In today's world, application growth is unprecedented and enterprise applications on a wide range of...

VMware NSX Advanced Load Balancer Benchmark Report
Moving from appliance-based load balancers to software-defined VMware NSX Advanced Load Balancers could...
Achieve Cloud Security Cost Savings Through SIEM Optimization
Tame Rising SIEM Costs and Complexity Do you worry that your SIEM is falling behind on efficiently handling...
BlackBerry Cyber Suite
The challenge of securing and protecting data and endpoints is not a new requirement, but today it is...

Securing Digital Innovation Demands Zero-trust Access
To accelerate business and remain competitive, CIOs are rapidly adopting digital innovation initiatives...

How to Tackle Ransomware by Managing Human Risk
CybSafe's analysis of ICO data finds the number of incidents of ransomware reported has doubled in a...
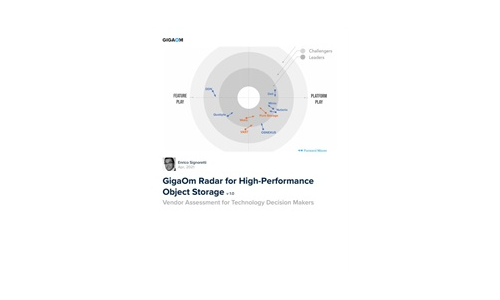
GigaOm Radar for High-Performance Object Storage
For quite some time, users have been asking for object storage solutions with better performance characteristics....
Building the digital workplace
The days when having a job meant traffic jams, cubicles, and a 9-to-5 schedule are coming to an end....

DDoS Threat Landscape Report: DDoS Trends from Q3 2022
DDoS attacks are growing larger, stronger, and more sophisticated. In Q3'22, we observed a resurgence...

2021 State of the Threat in review
The State of the Threat report is compiled by the world-renowned Secureworks® Counter Threat Unit™...

Box for banking and capital markets
One secure platform for banking and capital markets Easy, secure client experiences are the new gold...

Cybercrime tactics and techniques
2019 is off to an action-packed start in cybercrime. From a steadfast increase of pervasive Trojans to...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

