Internet of Things (IoT)

New Perspectives on Mobile Device Testing at a Global Scale
The old days of just translating the language in your app to make it readable to people in other countries...
Cloud Operating Model for Dummies
There's no denying we live in the cloud era. Organizations now deliver cloud services to help people...
How Virtual Desktop Infrastructure Enables Digital Transformation
Virtual desktop infrastructure (VDI) is a foundational technology that many organizations leverage as...
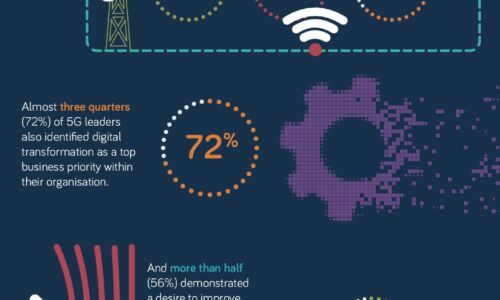
What makes a 5G Leader?
With 5G a still nascent technology, opportunity remains for businesses to accelerate adoption of this...

Securing high tech industry network data
We all understand the negative impact of data loss, so why is it that so many organisations seem to be...

5G in the Transport sector
The Transport sector is pioneering the adoption of 5G connectivity, and yet it's doing so with quiet...

2022 Threat Report
The BlackBerry 2022 Threat Report is not a simple retrospective of the cyberattacks of 2021. It is a...

The CISO’s Guide to Effective Zero-trust Access
Best practices in network access stipulate a zero-trust access (ZTA) approach. CISOs looking to implement...

How To Choose a Managed Extended Detection and Response Solution
Organizations face major cybersecurity hurdles. The first challenge is finding effective cybersecurity...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.