Data Center

Why you need an adaptive security segmentation solution
The threat landscape is more dynamic than ever before, and as business-critical applications traverse...

Back to the Basics: Cyber Hygiene Starts with Asset Management
The challenge: managing millions of dynamic, distributed and diverse assets while maintaining high standards...
Succeeding With Analytics in the Cloud
Enterprises today recognize that cloud is integral to their digital transformation. As organizations...

Cloud Clarity: Don’t Let Complexity Derail Your Digital Strategy
Cloud has never been more important to agile, responsive organisations, but the reasons for its appeal...

The Promise of XDR for Effective Threat Detection and Response
In October 2020, the Enterprise Strategy Group (ESG), completed a research survey of 388 cybersecurity...

The Digital Creator's Guide to the Wonderful World of Workstations
What you will learn from this Infobrief: Download now to find out more. Learn more about Dell Technologies...

5 Critical Considerations for DDoS Mitigation
Distributed denial-of-service (DDoS) attacks remain one of the most effective methods used by cybercriminals...

Business in the new economy landscape
How we coped with 2020 and looking ahead to a brighter 2021: The state of European midsized businesses. Medium-sized...
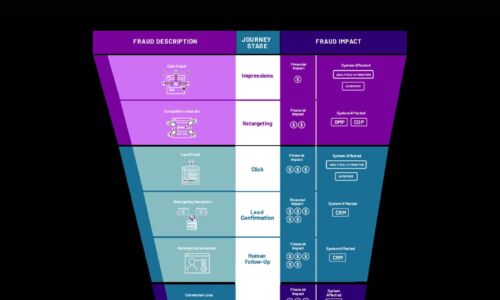
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....

Office of the CTO Report: Continuous API Sprawl
APIs are a contract between the service provider and service consumer. When any application uses an API,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.



